Rapid software development speed can often take precedence over security, leading to latent vulnerabilities that can be exploited before they are detected. This, in turn, leads to an increasing security risk as systems become larger and more complex. Organizations are transitioning from reactive measures to preemptive cybersecurity that integrates protection into all aspects of development.
This ensures that organizations will be able to protect data, keep their systems healthy and continue on a growth rocket. Structured security frameworks that align with modern software development practices can be implemented by companies like Aqlix.
Why Preemptive Security is a Growth Catalyst
Preventative cybersecurity is all about anticipating and preventing these risks from disrupting operations. Rather than responding to threats after they materialize, companies make security part of their development workflows from the start.
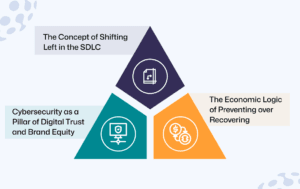
1. The Concept of Shifting Left in the SDLC
Shifting left means embedding security practices as early as possible in the software development life cycle. Vulnerabilities are detected at the design and coding level, not after deployment.
This avoids the expensive and complicated process of repairing later on. Thorough early testing, secure coding standards and automated checks prevent weaknesses from reaching production environments so that applications remain stable and secure as they grow.
2. Cybersecurity as a Pillar of Digital Trust and Brand Equity
Cybersecurity Best Practices Build Trust & Reputation with Customers When businesses prioritize the protection of data, they build trust and become a reliable partner for users and stakeholders.
Defensive action taken on the front foot minimizes the chances of data breaches and service disruptions. This reliability boosts brand value and deepens the relationships brands have with customers over decades, especially for industries that deal with sensitive information or financial transactions.
3. The Economic Logic of Preventing over Recovering
It’s much more costly to fix security problems after a breach than it is to prevent them in the first place. The recovery costs are downtime, legal, and reputational support.
Preemptive cyber security shifts the focus to prevention, as this is more cost efficient in the long term. There are a lot of features that come with investing in secure development as you can avoid unexpected costs, while providing reliable operations and service delivery.
Implementing a Preemptive Defense Framework
Designing a proactive cybersecurity strategy involves tools, processes, and architectural choices. Companies need to implement solutions that constantly monitor their systems and provide classified alerts on any potential threats.
1. Automated Vulnerability Scanning and Continuous Monitoring
Automated tools are vital for real-time vulnerability discovery. These systems scan codebases, dependencies and infrastructure for potential security issues before deployment.
Demonstrates AI driven monitoring solutions to analyze patterns and identifies anomalies that can indicate potential threats. By constantly monitoring systems, it helps ensure that even after deployment, all systems are protected and reduces the risk of live environments having undetected vulnerabilities.
2. Zero Trust Architecture & Microsegmentation
The foundation on which a zero trust architecture function is where no user or system should be trusted by default. There has to be a verification of every access request based on identity and context.
Microsegmentation is a security technique that divides the data center into multiple segments. This reduces the spread of potential network vulnerabilities, helping to ensure that compromised parts do not affect the entire system. Together, these strategies strengthen resilience in the system.
3. Integrating Secure API Gateways for Third Party Connectivity
Modern applications utilize external services and application programming interfaces (APIs) to deliver functionality. However, these integrations must be secured from unauthorized access and exposures.
This trend is driven by two things: the security best practices must be applied to APIs, and secure API gateways act as checkpoints over authentication, data validation, and traffic monitoring. They keep communication between systems secure while also supporting high levels of performance and reliability across connected platforms.
4. Regular Pen Testing/ Ethical Hacking
Penetration testing is a real world emulation of attacks against applications and their infrastructure to identify vulnerabilities. Ethical hackers deploy the same techniques but in a controlled environment to identify vulnerabilities that automated tools cannot find.
Organizations stay ahead of the evolving threats through regular testing. It analyzes actionable fingerprints that enhance system security, making sure defenses adapt to emerging attack vectors.
Measuring Resilience and Navigating Compliance
However, implementing these preemptive strategies will require ongoing assessment and advancements. They must monitor performance metrics, comply with industry standards, all while maintaining adaptability in their security strategy.

1. Measuring Resilience via Mean Time to Detect
In threat detection in a system, the mean time to detect becomes a prime metric. Better detection time means a better security mechanism.
This enables organizations to track their detection and response developments as a measure of the effectiveness of these proactive measures. Quick detection allows teams to act rapidly, limiting the potential impact of security incidents on operations.
2. Avoiding the Pitfall of Compliance Over Reliance
Regulations and industry-following rules will never ensure complete security though data protection is no doubt a good strategy. Most organizations tend to think that just meeting regulatory standards is enough for their systems.
In fact, it’s here where preemptive cybersecurity starts to differentiate itself from compliance and demonstrates a more proactive alternative in the form of dynamic security that organises around new threats. Compliance, while necessary, is the lowest standard; businesses must always look to improve their security strategies and expectations to match new threats.
Conclusion
This is where proactive cybersecurity becomes necessary for businesses that want to scale their software infrastructure without sacrificing security. When organizations bake protection into every phase of development, they significantly lower risk and prevent disruptions to operations.
Taking a proactive approach helps to ensure that applications are protected against changing threats, and allows for long term growth. Through Aqlix IT Solutions, businesses can adopt secure development practices that not only preserve digital assets but also facilitate business growth in the long run.”
Frequently Asked Questions
What is preemptive cybersecurity?
A precursor to Cybersecurity where we look out for threats before they happen, this model of prevention, as the name suggests is called Preemptive cybersecurity. This means bringing security at the beginning of software development and continuously monitoring systems for vulnerabilities and risks before they can lead to a disruption of operations or data breaches.
How does shifting left improve software security?
The left shifting enhances security as vulnerabilities are identified in the early days of development stages. Secure coding is used by developers, and testing is done before deployment. This helps prevent security scars from reaching production and reduces the cost and complexity of fixing problems further down in the dev lifecycle.
What is zero trust architecture in cybersecurity?
In Zero trust architecture, no user or system is trusted by default. Authentication should be done against identities plus context on every access request. This provides a layer of security against unauthorized access and reduces the impact of potential breaches across an organization’s digital ecosystem.
Why is continuous monitoring important in cybersecurity?
Continuous monitoring programs enable organizations to identify threats and vulnerabilities as they occur. Almost every device that can connect to a network will have automated tools which analyze system activity and identify any unusual behavior that may indicate a potential security risk. This assists organizations in the swift response to incidents and maintaining a secure environment even after running applications.
Can AI improve cybersecurity strategies?
Yes. AI Powered tools facilitate automation of detections, anomaly analysis, and time to response. These capabilities enable organizations to enhance their security environments and respond effectively to changing cyber threats.